🇬🇧 English version of this article.
Wir freuen uns bekannt zu geben, dass BusKill-Kabel zum ersten Mal persönlich in einem Ladengeschäft in Deutschland (Leipzig) gekauft werden kann.
🇬🇧 English version of this article.
Wir freuen uns bekannt zu geben, dass BusKill-Kabel zum ersten Mal persönlich in einem Ladengeschäft in Deutschland (Leipzig) gekauft werden kann.
🇩🇪 Deutsche Version dieses Artikels
We’re happy to announce that, for the first time ever, BusKill cables can be purchased in-person in Leipzig, Germany.
The BusKill project has partnered with ProxyStore to make BusKill laptop kill cords finally available from a brick-and-mortar location. You can now go to the following location and purchase a BusKill cable with cash or cryptocurrency.
Wolfgang-Heinze-Str. 14
04277 Leipzig
Germany
We’re happy to announce that we were successfully able to initiate a BusKill lockscreen trigger using a 3D-printed BusKill prototype!
While we do what we can to allow at-risk folks to purchase BusKill cables anonymously, there is always the risk of interdiction.
We don’t consider hologram stickers or tamper-evident tape/crisps/glitter to be sufficient solutions to supply-chain security. Rather, the solution to these attacks is to build open-source, disassembleable, and easily inspectable hardware whose integrity can be validated without damaging the device and without sophisticated technology.
Actually, the best way to confirm the integrity of your hardware is to build it yourself. Fortunately, printing your own circuit boards, microcontroller, or silicon has a steeper learning curve than a BusKill cable — which is essentially just a USB extension cable with a magnetic breakaway in the middle.
Mitigating interdiction via 3D printing is one of many reasons that Melanie Allen has been diligently working on prototyping a 3D-printable BusKill cable this year. In this article, we hope to showcase her progress and provide you some OpenSCAD and .stl files so you can experiment with building your own and help test and improve our designs.
ⓘ Note: This post is adapted from its original article on Melanie Allen’s blog.
Last month, I successfully triggered a lockscreen event using our 3D-printed BusKill prototype.
We’re happy to announce the release of BusKill v0.7.0
Most importantly, this release allows you to arm the BusKill GUI app such that it shuts-down your computer when the BusKill cable’s connection to the computer is severed.
We’re happy to announce that we’ve had good progress on the design of the 3D printable BusKill USB-A magnetic breakaway couplers this year!
While we do what we can to allow at-risk folks to purchase BusKill cables anonymously, there is always the risk of interdiction.
We don’t consider hologram stickers or tamper-evident tape/crisps/glitter to be sufficient solutions to supply-chain security. Rather, the solution to these attacks is to build open-source, disassembleable, and easily inspectable hardware whose integrity can be validated without damaging the device and without sophisticated technology.
Actually, the best way to confirm the integrity of your hardware is to build it yourself. Fortunately, printing your own circuit boards, microcontroller, or silicon has a steeper learning curve than a BusKill cable — which is essentially just a USB extension cable with a magnetic breakaway in the middle.
Mitigating interdiction via 3D printing is one of many reasons that Melanie Allen has been diligently working on prototyping a 3D-printable BusKill cable this year. In this article, we hope to showcase her progress and provide you some OpenSCAD and .stl files so you can experiment with building your own and help test and improve our designs.
ⓘ Note: This post is adapted from its original article on Melanie Allen’s blog.
A few years ago, Michael asked me if I was interested in developing a 3D-printed case for the magnetic breakaway. He enumerated the following design requirements:
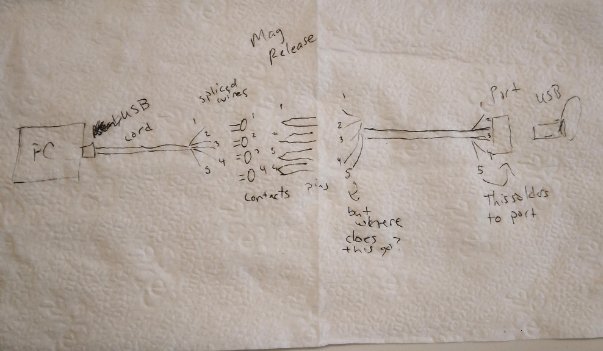
However, over the past years’ iterations, we adjusted the requirements:
In celebration of Bitcoin Black Friday 2022, we’re offering a 10% discount on all BusKill cables sold between Nov 19 to Dec 04.
We’re happy to announce the release of BusKill v0.6.0
Most importantly, this release allows you to arm the BusKill app such that it shuts-down your computer when the BusKill cable’s connection to the computer is severed.
You can upgrade your BusKill app to the latest version either by
We’re excited to announce that our first production run of BusKill cables is now in-stock in our distribution center.
The first BusKill prototype was born in 2017. It gained international popularity in 2020 when Michael Altfield described how to build your own BusKill cable. After extensive effort and with the help of several contributors, a Linux hacker’s DIY cable got a user-friendly, cross-platform GUI.
When the only USB-A magnetic breakaway coupler on the market became out of stock and EOL’d, we raised $18,507 on CrowdSupply in early 2022 to manufacture our own injection-molded cable. One thousand logistics challenges later, Mouser started shipping BusKill cables to our backers in October 2022.
Now that the hardware is out the door, we’re hard at work on new features for the BusKill app. Our top goal is to add a soft-shutdown trigger to the existing lock-screen trigger. At the time of writing, this is functional on Linux and Windows. We’re just working out the kinks of privilege escalation on MacOS.
To be notified when we’ve added the soft-shutdown trigger to the BusKill app, you can signup for our newsletter.
We did our best to test BusKill across the three target platforms, but the wide spread of OS versions does leave room for error. If you happen to find a bug with BusKill, please let us know.
If you don’t have a BusKill cable yet, you can buy one here on this website or build your own. And for the makers out there, checkout the progress on our 3D printable BusKill magnetic breakaway coupler 🙂
You can also buy a BusKill cable with bitcoin, monero, and other altcoins directly from our BusKill Store
We’re happy to announce the release of BusKill v0.5.0
You can upgrade your BusKill app to the latest version either by
Watch the below video to see a demonstration of BusKill running on all of the below-listed systems.
Can’t see video above? Watch it on PeerTube or on YouTube at youtu.be/g6eT8JSIgjw
Transparency is important. As we launch our crowdfunding campaign (making the BusKill cable available for purchase for the first time), we wanted to provide a clear video demo showing the cable in-use in all tested platforms:
BusKill was tested to work in Windows 10.
Visit docs.buskill.in for instructions on how you can build your own BusKill cable and download the BusKill app for Windows.
Or you can buy a BusKill kit with the BusKill Windows app pre-installed on the the included USB drive.
BusKill was tested to work in MacOS 10.15 (Catalina).
Visit docs.buskill.in for instructions on how you can build your own BusKill cable and download the MacOS .dmg release.
Or you can buy a BusKill kit with the BusKill MacOS app pre-installed on the the included USB drive.
BusKill was tested to work in Ubuntu Linux.
Visit docs.buskill.in for instructions on how you can build your own BusKill cable and download the Linux .AppImage release.
Or you can buy a BusKill kit with the BusKill Linux app pre-installed on the the included USB drive.
BusKill was tested to work with TAILS (The Amnesic Incognito Live System).
While you could use the BusKill Linux .AppImage release with a second USB drive while using TAILS, the recommended solution for security-critical users is to just use the BusKill cable in-line with the TAILS live USB drive. This takes advantage of
Visit docs.buskill.in for instructions on how you can build your own BusKill cable to use with TAILS.
Or you can buy a BusKill cable to support the BusKill project.
BusKill was also tested to work with QubesOS.
Due to the design of QubesOS (dom0, sys-usb, etc), the BusKill GUI app does not support QubesOS. Instead, QubesOS support is implemented using the qubes-rpc and a set of scripts stored in sys-usb and dom0.
For more information on how to use BusKill in QubesOS, see our BusKill guide for QubesOS.
Visit docs.buskill.in for instructions on how you can build your own BusKill cable to use with QubesOS.
Or you can buy a BusKill cable to support the BusKill project.